PREVIOUS ARTICLENEXT ARTICLE
NEWS
The Flame infrastructure highly sophisticated
By Staff Writer 5 June 2012 | Categories: news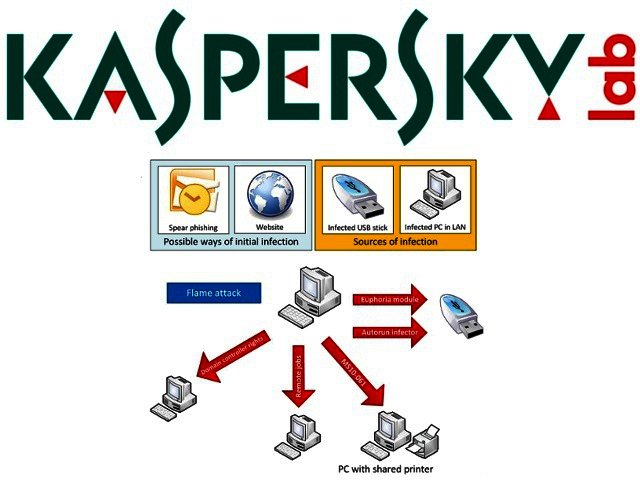
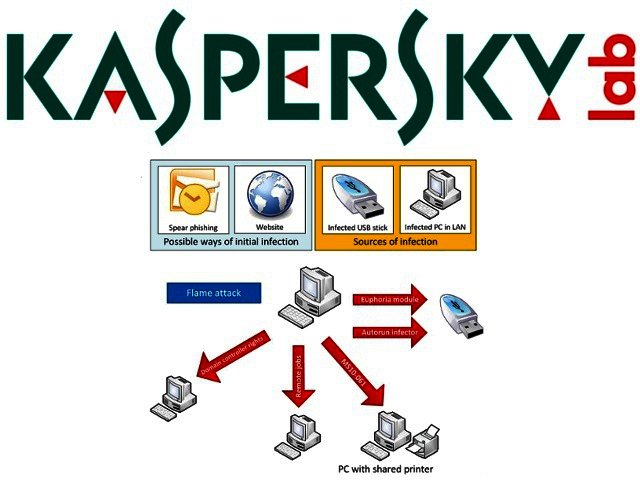
After last week’s announcement regarding the discovery of a highly sophisticated malicious program, known as The Flame, Kaspersky Lab believes they have made some progress combating the threat.
The Flame was actively being used as a cyber-weapon targeting entities in several countries; in collaboration with GoDaddy and OpenDNS, Kaspersky Lab succeeded in sinkholing most of the malicious domains used by The Flame’s Command and Control (C&C) infrastructure. Sinkholing usually refers to the process of directing infected computers away from the C&C centre to systems owned by the analytics company.
Kaspersky Lab has been closely monitoring the C&C infrastructure of The Flame and has published a detailed research post today about the findings.
The following details summarise the results of the analysis, and paints an interesting picture of the intelligence of The Flame operation:
• The Flame C&C infrastructure, which had been operating for years, went offline immediately after Kaspersky Lab disclosed the discovery of the malware’s existence last week.
• Currently there are more than 80 known domains used by Flame for C&C servers and its related domains, which have been registered between 2008 and 2012.
• During the past four years, servers hosting the Flame C&C infrastructure moved between multiple locations, including Hong Kong, Turkey, Germany, Poland, Malaysia, Latvia, the United Kingdom and Switzerland.
• The Flame C&C domains were registered with an impressive list of fake identities and with a variety of registrars, going back as far as 2008.
• According to Kaspersky Lab’s sinkhole, infected users were registered in multiple regions including the Middle East, Europe, North America and Asia-Pacific.
• The Flame attackers seem to have a high interest in PDF, Office and AutoCad drawings.
• The data uploaded to the Flame C&C is encrypted using relatively simple algorithms. Stolen documents are compressed using open source Zlib and modified PPDM compression.
• Windows 7 64 bit, which Kaspersky Lab previously recommended as a good solution against infections with other malware, seems to be effective against Flame
The Flame was discovered by Kaspersky Lab’s experts during an investigation prompted by the International Telecommunication Union (ITU), and the analysis of the malicious program revealed it was the largest and most complex attack toolkit to date.
Kaspersky Lab’s analysis of the malware revealed that it was currently being used for cyber-espionage, and that it would infect computers to steal data and sensitive information. The stolen data was then sent to one of The Flame’s C&C servers.
To read the full analysis of The Flame’s C&C infrastructure and all its technical details, please visit Securelist.
USER COMMENTS
Most Read Articles
Read

Magazine Online
TechSmart.co.za is South Africa's leading magazine for tech product reviews, tech news, videos, tech specs and gadgets.
Start reading now >
Download latest issue
Have Your Say
What new tech or developments are you most anticipating this year?
New smartphone announcements (46 votes)
Technological breakthroughs (29 votes)
Launch of new consoles, or notebooks (14 votes)
Innovative Artificial Intelligence solutions (29 votes)
Biotechnology or medical advancements (24 votes)
Better business applications (160 votes)



